Hello,
to my knowledge there are 2 options for creating a SSH key from an existing OpenPGP key:
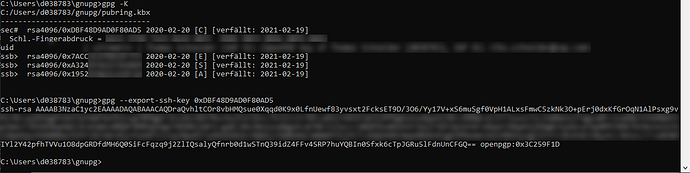
- generating Pageant-PublicKeys.txt when plug-in stick
- gpg --export-ssh-key
When I compare the keys generated by these options I don’t think they are consistent.
Please check the details below:
In file Pageant-PublicKeys.txt the key looks different, though.
This raises the following questions:
- Why are the keys different?
- Which one is the correct one to be used for SSH authentication?
THX
You are using two different keys to generate the public ssh-key ( with pageant the sign key, with gpg authentication key) gpg --card-status will show you the key id for the key that is normally used for authentication (in your case the 3rd one) . So you should use this key and export that as public ssh-key. BUT you could also use one of the other two keys for ssh: just export the public key and put it remote in ~/.ssh/authorized_keys . remote ssh will use this key and challenge local ssh/NK . If you put more than one key from the NK into authorized_keys, to my experience always the last key is used.
2 Likes
 iirc it is always the first match. But other than that nice explaination, thanks.
iirc it is always the first match. But other than that nice explaination, thanks.